Get verified customer data. Without the friction.
Millions of customers already have a verified vault. One click and you receive what you need. No back-and-forth, nothing exposed. The infrastructure is already running. You just connect.
Why Geena
Your customers hate the paperwork. Your legal team hates the breach risk.

3
Reminder emails
Per client, on average, just to collect a single ID document
50%
of ops time
Spent chasing documents, not reviewing them
9
organisations
Receive the same identity data from the same person, every year
“We were sending three reminder emails per customer just to get a copy of their ID. Three. Most of them had already given it to someone else that month.”
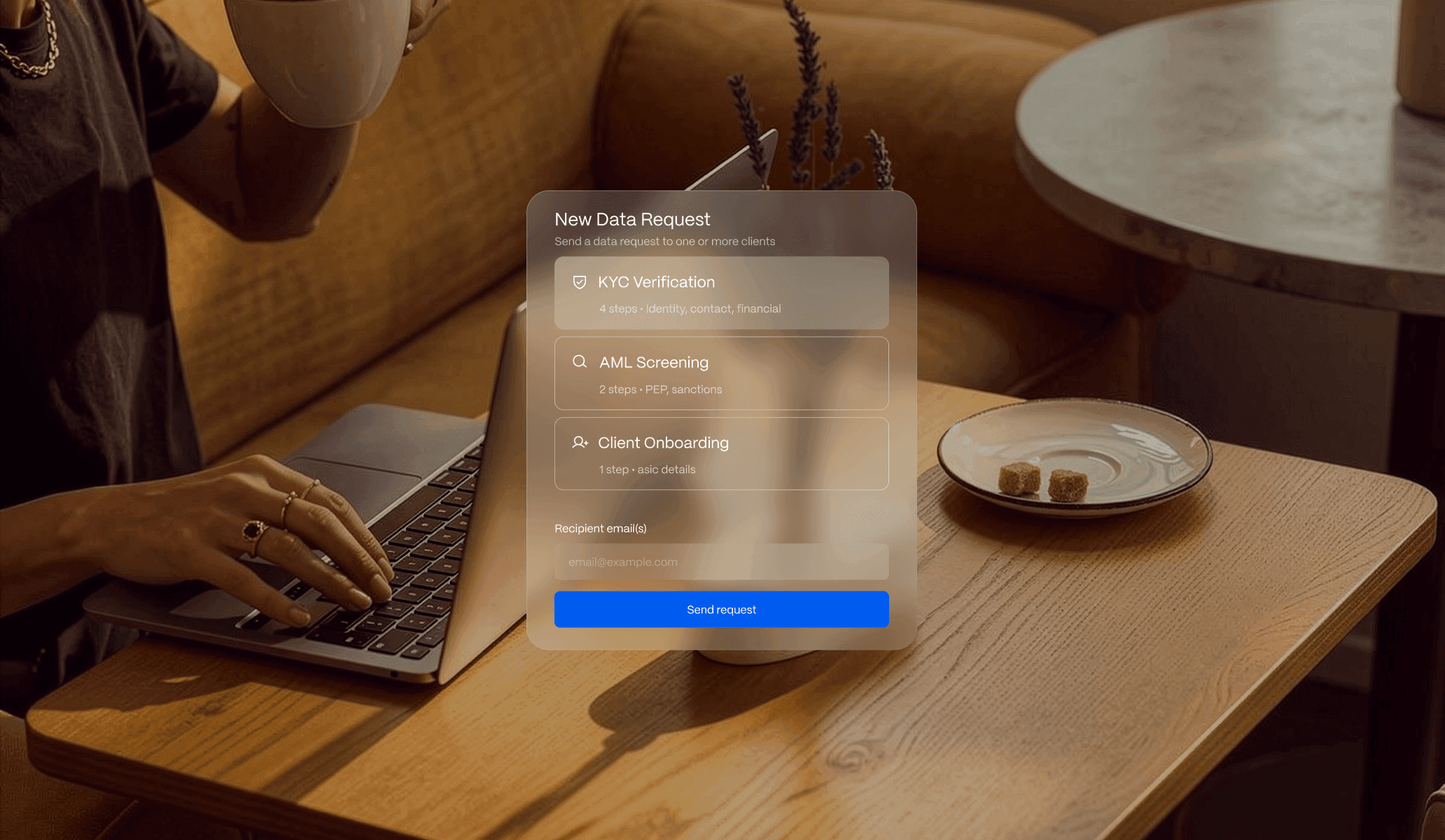
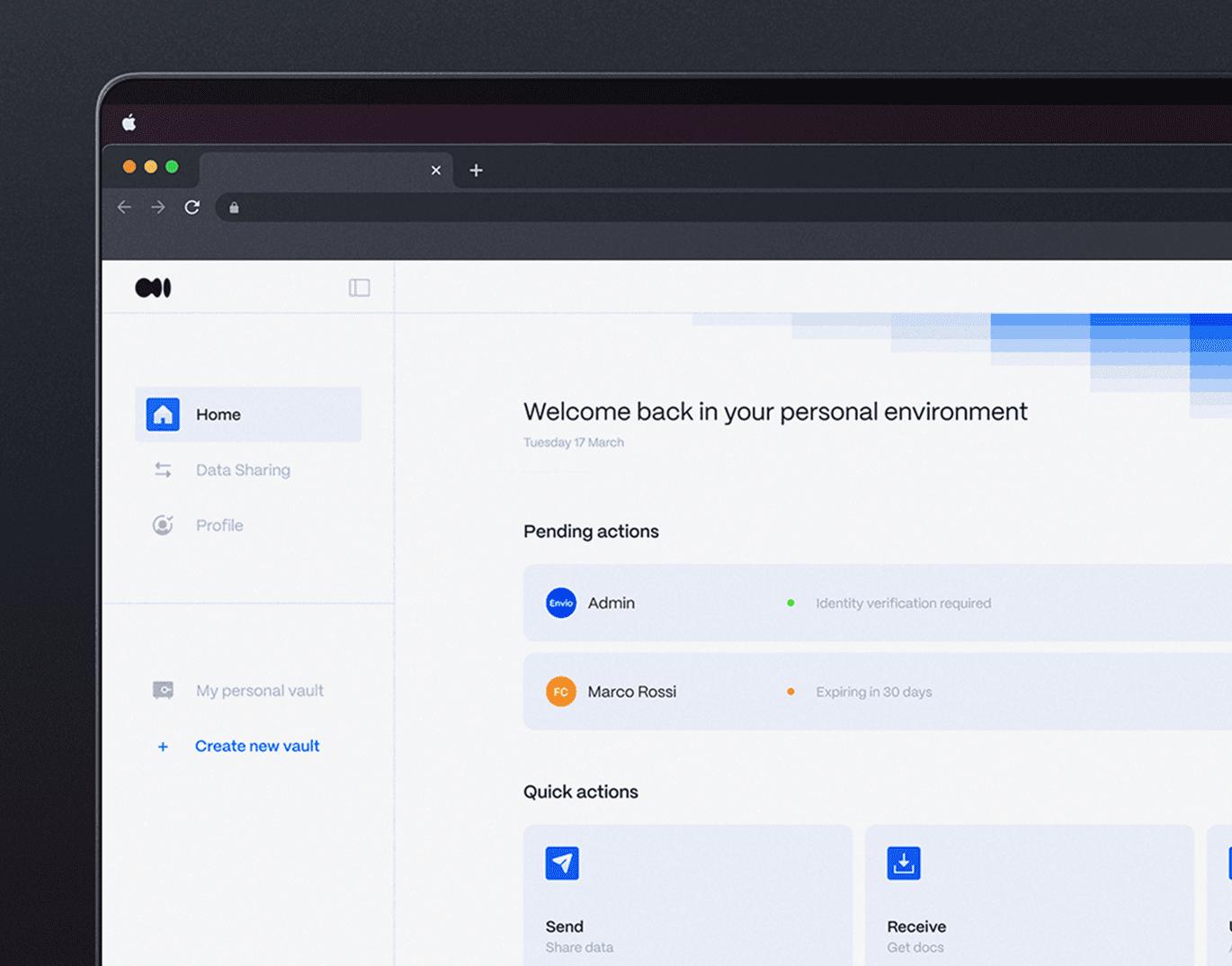
How it works
One request. One tap. Verified data delivered.
“I set up a new data request for our insurance product in the time it took to finish my coffee. No developer needed, no Jira ticket.”
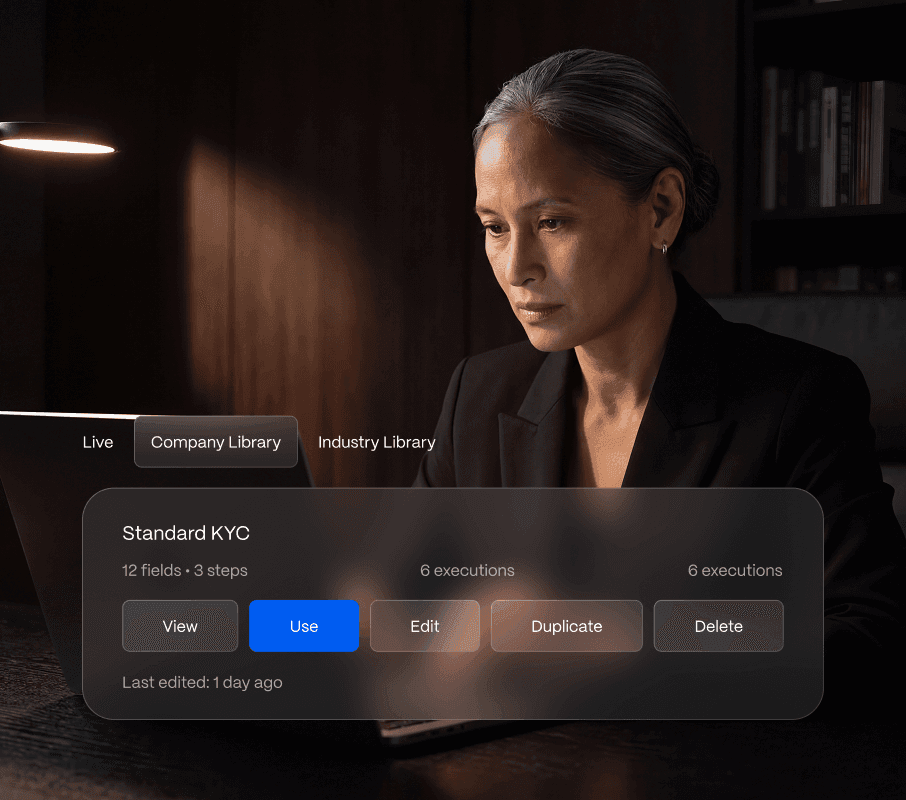
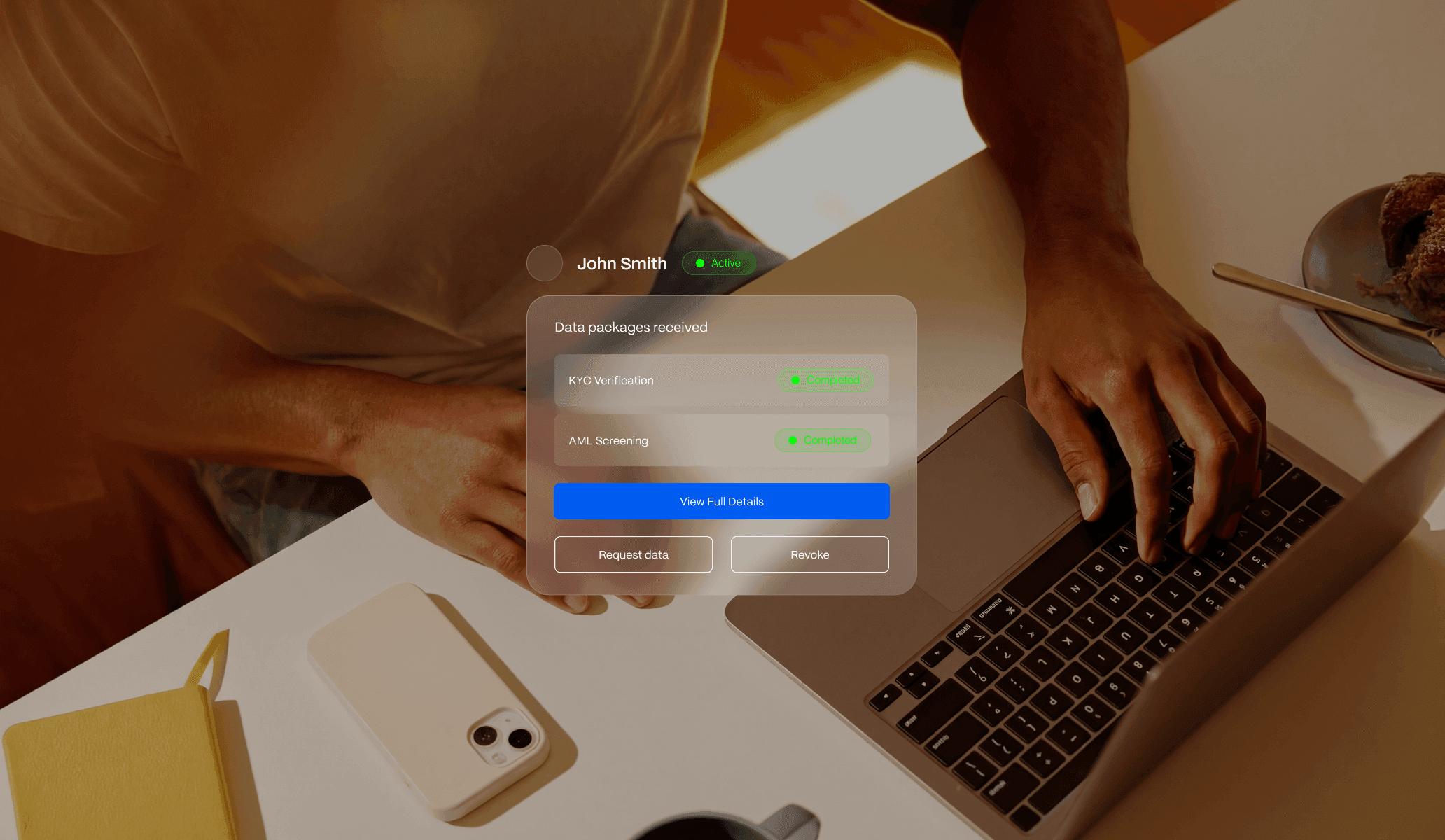
Compliance
Full visibility. Zero document liability
Your process. Your rules. We handle the rest.
“I sleep better not having customer passport scans sitting on our servers. That was a genuine concern.”
You shouldn't be building this.
You're not an identity company. So why is your team chasing PDFs over email and storing documents you never asked for?
You're not an identity company. So why is your team chasing PDFs over email and storing documents you never asked for?
No manual checks needed.
More clients, lower cost.
People finish because it's easy.
Build flows without a developer.
Clients see you, not us.
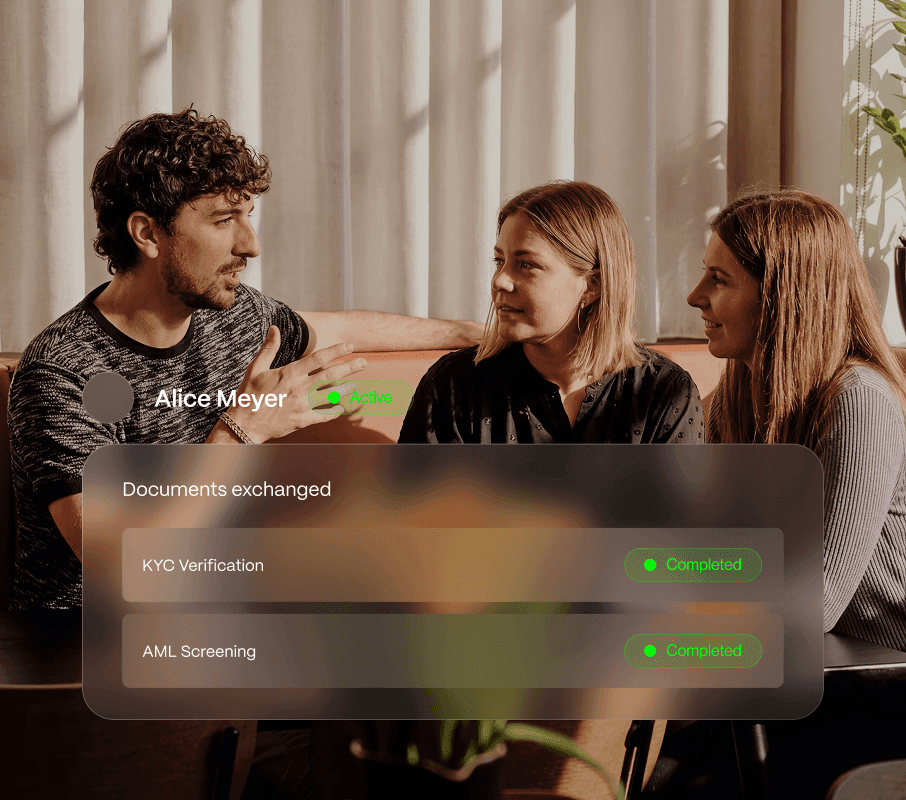
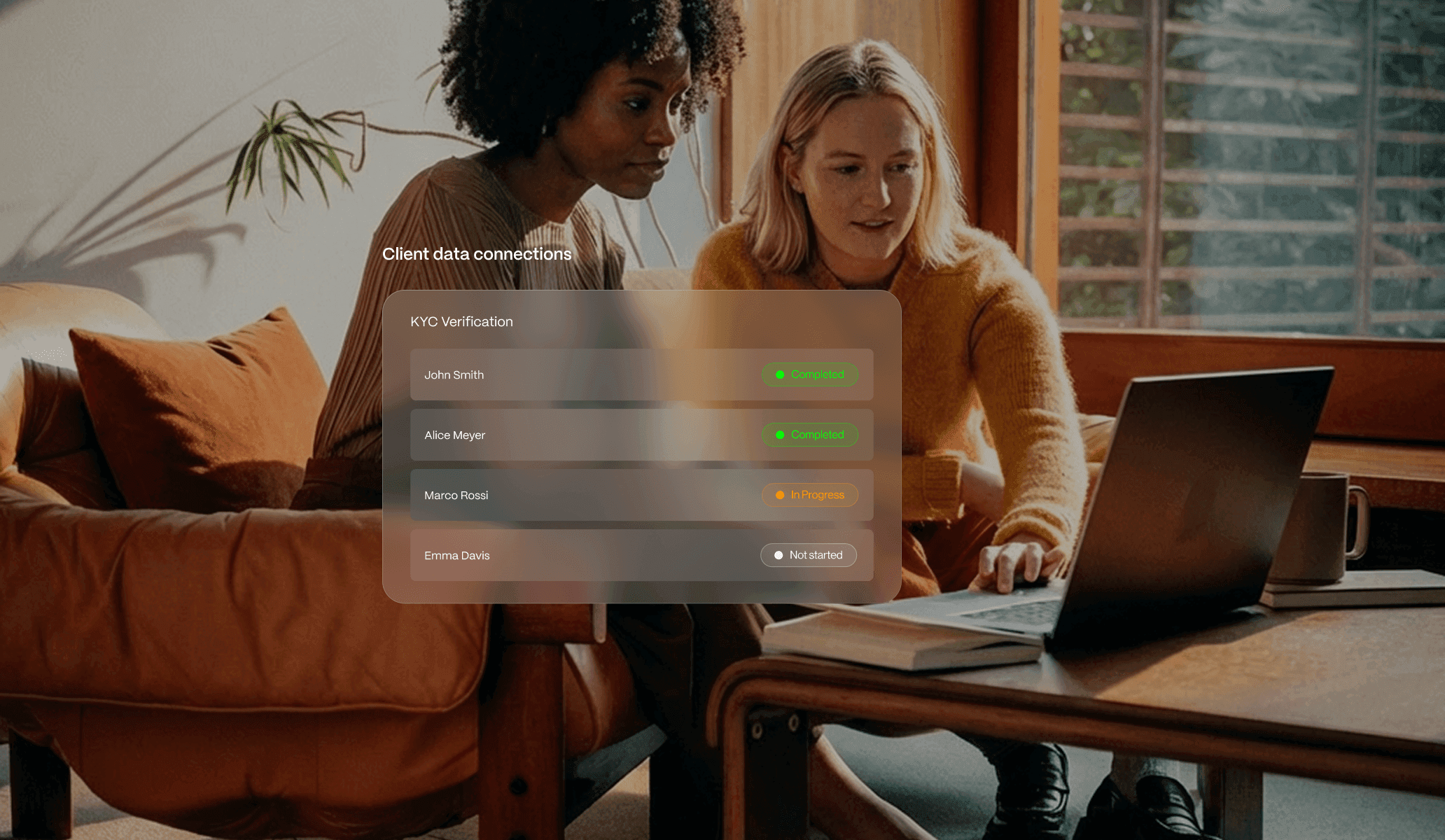
One platform. Two sides of every transaction.

For you
Renting, subscribing, investing, applying. Verify your identity once and share instantly, whether it's a car rental or a fund administrator.

For businesses
Collect verified identity data without storing sensitive documents. Your clients share from their vault. You get what you need.